The dark web network infrastructure enables multi-layer encryption to prevent location tracking and preserves confidentiality among dark web users and hosts. Like the other blogs in our dark web series, our primary reference is the Department of Justice’s Cyber Security Unit guidance to the private sector on gathering cyberthreat intelligence in dark marketplaces. Every year, cybersecurity threats evolve—with buzzwords like ransomware, DDoS, and man-in-the-middle attacks making headlines. This helps automate alerting, enrich existing intelligence, and reduce the manual effort involved in tracking threat actors.
The dark web is often shrouded in mystery and misconceptions, leading many to approach it with apprehension. In this article, we will explore what the dark web truly is, how to access the dark web, and the potential benefits and dangers that come with it. By understanding this hidden part of the internet, individuals can make informed decisions and navigate it safely, if necessary.
Understanding the Dark Web
If you’re just browsing or doing legitimate research, accessing the dark web is fine. Huntress gives you fully managed endpoint detection and response (EDR), so you've got 24/7 support from security experts ready to respond to threats. Threats can seem overwhelming, but with our in-depth understanding of how threat actors think, we know what to look for. It’s incredible to see just how many parallels exist between anyone with a “normal” day job and dark web threat actors. That’s right—threat actors have their very own court system, along with codes of conduct to follow to minimize the chances of landing there themselves.
The dark web is a portion of the internet that is not indexed by traditional search engines. It requires specific software and configurations to access, the most common being the Tor browser. This segment of the web is known for its anonymity, allowing users to browse and communicate without revealing their identity. While it has received negative attention for illegal activities, the dark web also serves as a space for privacy advocates, journalists, and others seeking to discuss sensitive topics freely.
How to Access the Dark Web
To access the dark web, follow these steps:
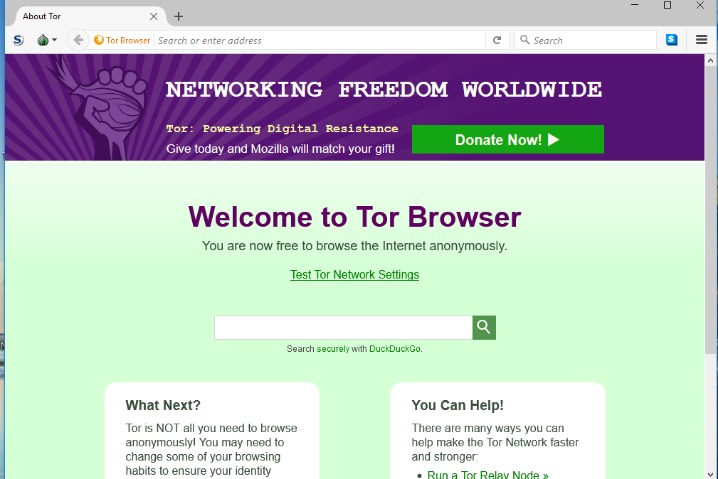
- Download the Tor Browser: Visit the official Tor Project website and download the browser designed for secure and anonymous browsing.
- Install and Configure: Follow the installation instructions, ensuring you keep the default settings to maintain privacy.
- Connect to the Tor Network: Open the Tor Browser, and it will automatically connect you to the Tor network, where you can start browsing.
- Visit .onion Sites: Use links that end in .onion, which denote websites specifically designed for access through the Tor network.
Benefits of the Dark Web
While often highlighted for its illicit activities, the dark web has legitimate uses that can be beneficial:
- Privacy: The dark web provides a platform for individuals to communicate without fear of surveillance, crucial for whistleblowers and journalists.
- Access to Information: Users can find information on sensitive topics that may be censored in their home countries, allowing for informed decision-making.
- Support for Activism: Activists can share ideas and organize movements without risking their safety or freedom.
Risks Involved
Despite its potential benefits, navigating the dark web comes with inherent risks:
- Legal Consequences: Engaging in illegal activities can lead to severe legal repercussions.
- Security Threats: The risk of encountering malicious software is higher on the dark web, making security measures essential.
- Scams and Fraud: Users may fall victim to scams due to the lack of regulation and oversight on this portion of the internet.
Staying Safe While Exploring
- Simple interface makes searches straightforward and distraction-free
- The dark web evolved from a thesis project of a University of Edinburgh student named Ian Clarke, who wanted to create a new way to send anonymous communication online.
- Scripts are a common method for identifying or exploiting visitors on hidden sites.
- Understanding the dark web vs surface web comparison helps clarify internet architecture.
- But, perhaps a big surprise to anyone thinking the Dark Web is just for criminal activity, it can also be leveraged for legitimate purposes.
- Cybercrime is getting more sophisticated, putting businesses at a serious disadvantage when it comes to protecting their networks.
If you decide to explore the dark web, prioritize your safety by following these guidelines:
- Use a VPN: A Virtual Private Network adds an extra layer of security and anonymity.
- Don't share personal information: Avoid providing any details that could be used to identify you.
- Stick to known links: Only visit reputable sites to reduce the risk of encountering harmful content.
- When accessing the dark web, safety needs to be a top priority.
- "If you access 'facebookcore' you are definitely connected to Facebook, because of the nature of Onion addressing — no DNS or Certificate Authority censorship mechanisms are applicable."
- The Tor Browser provides anonymity and privacy by routing your internet connection through a network of volunteer-operated servers around the world.
- While you do need a special browser to access the dark web, it may surprise people to learn that no special hardware or technical skills are required.
- IOS users depend on Onion Browser when they need quick, private access without desktop tools.
Conclusion
Understanding how to access the dark web and the consequences of doing so is crucial for anyone considering entering this hidden part of the internet. While it offers unique opportunities for communication and information access, it also poses significant risks. By approaching the dark web with caution and awareness, individuals can navigate its complexities safely.

