These threats underscore why proactive dark web monitoring is essential for cybersecurity teams. Because indexing is incomplete and unreliable, users often rely on community-shared lists, verified directories, and forum recommendations to locate legitimate sites. Despite the dark web’s anonymity, users still need tools to navigate its vast and often confusing landscape. Users should assume that illegal activity can be traced despite Tor, I2P, or other privacy networks.
The search engine itself might be safe, but the links it gives you might not be. Unfiltered engines Torch, Haystak, etc. will display everything, including scam sites or malware laced pages these are only as safe as your own caution. However, no search engine can make the dark web 100% safe there’s always a risk in clicking unknown links.
Here are the key use cases, pros, and cons between the most common dark web services (Tor, ZeroNet, I2P, and Freenet). The inconvenience of the darknet infrastructure is outweighed by the security it provides. While it was originally used by dissidents to circumvent censorship laws, it is now popularly used by cyber criminals to offload stolen and malicious content.
The internet is a vast expanse of information, but not all of it is accessible through traditional search engines like Google. Among the untouched layers lies the dark web, a space often shrouded in mystery and misconceptions. Understanding how to access the dark web can equip individuals with knowledge that is crucial in today's digital age, whether for privacy concerns, research purposes, or simply curiosity. This article aims to shed light on the essentials of navigating this hidden part of the internet safely and responsibly.

Access The Dark Web
The dark web refers to the portion of the internet that isn't indexed by traditional search engines. It requires specific software to access, the most popular being Tor (The Onion Router). Tor allows users to connect to websites with .onion domains, which provide anonymity for both users and site operators.
What You Need to Access the Dark Web
To access the dark web, you will need the following:
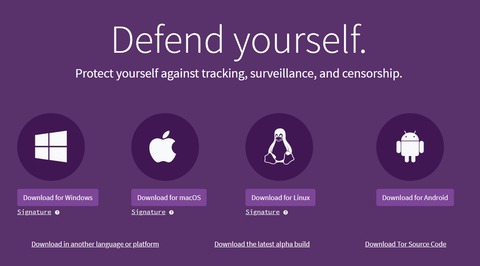
- Tor Browser: This is the primary tool required to navigate the dark web. It encrypts your internet traffic and helps maintain anonymity.
- VPN Service: While not mandatory, using a Virtual Private Network (VPN) in conjunction with Tor can provide an additional layer of security.
- Safety Practices: Understanding safe browsing habits on the dark web is crucial. Avoid sharing personal information and be cautious of links to untrusted sites.
Steps to Access the Dark Web
- Start by downloading the Tor browser, which is necessary to access dark web sites.
- The vast portion of the internet not indexed by search engines, including private databases and password-protected sites, which are primarily used for legitimate, secure data storage.
- Several dark web search engines have been developed to index and provide access to hidden services.
- Called "Silk Road 2.0", the relaunched site promised improved security to avoid another shutdown.
- It’s also important to note that these prices are for illegal transactions, and engaging in such activities is against the law and can result in severe penalties.
- Download the Tor Browser: Go to the official Tor Project website to download the browser securely.
- Install and Set Up: Follow the installation instructions, ensuring your internet connection is stable.
- Connect to Tor: Once installed, open the Tor browser and connect to the Tor network. This may take a few moments.
- Find Dark Web Links: Since these sites don’t appear on regular search engines, accessing directories like the Hidden Wiki can help guide you to a few legitimate sites.
Safety Considerations
While accessing the dark web, safety should always be your top priority:
- Stay Anonymous: Use a pseudonym and avoid revealing any personally identifiable information.
- Avoid Illegal Activities: The dark web can host illegal marketplaces. Engaging in these can lead to serious legal consequences.
- Use Security Software: Ensure your device is protected with antivirus software to guard against malware.
Why Access the Dark Web?
There are various reasons one might want to access the dark web, including:
- Research Purposes: Academics and researchers may study the dynamics of anonymity and information exchange in these spaces.
- Privacy Advocacy: Activists, especially in oppressive regimes, utilize the dark web to communicate safely and share information without surveillance.
- Exploration: Many are simply curious about this hidden facet of the internet and wish to understand its workings.
- For many, Tor is synonymous with the dark web — the unindexed part of the internet that’s only accessible with certain browsers.
- The Dark Web is a place where sellers of illegal drugs, identities, information (passwords, account numbers, etc.) weapons, and many other illegal forms of physical materials and digital information look to traffic these materials across borders.
- This makes it possible for users to access the deep web without worrying about their browser history or behavior being monitored.
- Knowing how the dark web and deep web differ and overlap helps companies create better security strategies.
Conclusion
Accessing the dark web can be an enlightening experience when approached with caution and respect for legal boundaries. As digital privacy becomes increasingly important, understanding the mechanics and implications of the dark web is vital for any informed internet user. Remember to prioritize safety and make educated decisions while navigating this enigmatic part of the internet.